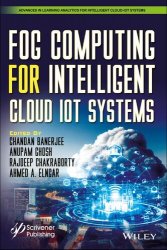
Название: Internet of Things Vulnerabilities and Recovery Strategies
Название: Internet of Things Vulnerabilities and Recovery StrategiesАвтор: Faheem Syeed Masoodi, Alwi M. Bamhdi, Majid A. Charoo, Zubair Sayeed Masoodi
Издательство: CRC Press
Год: 2025
Страниц: 355
Язык: английский
Формат: pdf (true)
Размер: 21.1 MB
The Internet of Things (IoT) is a widely distributed and networked system of interrelated and interacting computing devices and objects. Because of IoT’s broad scope, it presents unique security problems, ranging from unsecure devices to users vulnerable to hackers. Presenting cutting- edge research to meet these challenges, Internet of Things Vulnerabilities and Recovery Strategies presents models of attack on IoT systems and solutions to prevent such attacks. The book takes a holistic approach that encompasses visibility, segmentation, and protection. In addition to visual approaches and policy- driven measures, the book looks at developing secure and fault- tolerant IoT devices. It examines how to locate faults and presents mitigation strategies, as well as security models to prevent and thwart hacking. The book also examines security issues related to IoT systems and device maintenance. Whether you're a seasoned researcher, a dedicated practitioner, or a policymaker concerned with safeguarding our digital future, this book offers a comprehensive guide to navigating the intricate landscape of IoT vulnerabilities.